Web Application Vulnerability Scanners are automated tools that scan web applications, normally from the outside, to look for security vulnerabilities such as Cross-site scripting, SQL Injection, Command Injection, Path Traversal and insecure server configuration. This category of tools is frequently referred to as Dynamic Application Security Testing (DAST) Tools. A large number of both commercial and open source tools of this type are available and all of these tools have their own strengths and weaknesses. If you are interested in the effectiveness of DAST tools, check out the OWASP Benchmark project, which is scientifically measuring the effectiveness of all types of vulnerability detection tools, including DAST.
W3AF
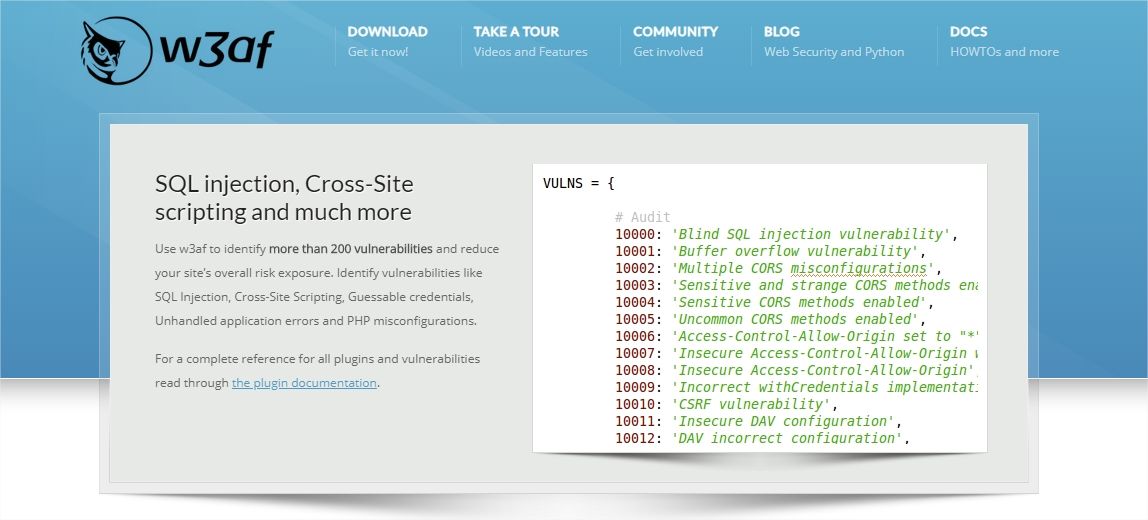
w3af is an open source web application used for security scanning. It is also called web application attack or audit framework. This application provides vulnerabilities scanner and exploiting tools for web applications. This project play an important role in penetration testing engagement because it’s provide information about security vulnerabilities.
Fast HTTP Client
- Proxy support
- HTTP Basic and Digest authentication
- UserAgent faking
- Add custom headers to requests
- Cookie handling
- HTTP response cache
- DNS cache
- File upload using multipart
Fuzzing
- Query string
- POST-data
- Headers
- Cookie values
- Multipart/form file content
- URL filename
- URL path
Nikto
Nikto is an Open Source (GPL) web server scanner which performs comprehensive tests against web servers for multiple items, including over 6700 potentially dangerous files/programs, checks for outdated versions of over 1250 servers, and version specific problems on over 270 servers. It also checks for server configuration items such as the presence of multiple index files, HTTP server options, and will attempt to identify installed web servers and software. Scan items and plugins are frequently updated and can be automatically updated.
Nikto is not designed as a stealthy tool. It will test a web server in the quickest time possible, and is obvious in log files or to an IPS/IDS. However, there is support for LibWhisker’s anti-IDS methods in case you want to give it a try (or test your IDS system).
Not every check is a security problem, though most are. There are some items that are “info only” type checks that look for things that may not have a security flaw, but the webmaster or security engineer may not know are present on the server. These items are usually marked appropriately in the information printed. There are also some checks for unknown items which have been seen scanned for in log files.
Features
- SSL Support (Unix with OpenSSL or maybe Windows with ActiveState’s Perl/NetSSL)
- Full HTTP proxy support
- Checks for outdated server components
- Save reports in plain text, XML, HTML, NBE or CSV
- Template engine to easily customize reports
- Scan multiple ports on a server, or multiple servers via input file (including nmap output)
- LibWhisker’s IDS encoding techniques
- Easily updated via command line
- Identifies installed software via headers, favicons and files
- Host authentication with Basic and NTLM
- Subdomain guessing
- Apache and cgiwrap username enumeration
- Mutation techniques to “fish” for content on web servers
- Scan tuning to include or exclude entire classes of vulnerability checks
- Guess credentials for authorization realms (including many default id/pw combos)
- Authorization guessing handles any directory, not just the root directory
- Enhanced false positive reduction via multiple methods: headers,
- page content, and content hashing
- Reports “unusual” headers seen
- Interactive status, pause and changes to verbosity settings
- Save full request/response for positive tests
- Replay saved positive requests
- Maximum execution time per target
- Auto-pause at a specified time
- Checks for common “parking” sites
- Logging to Metasploit
- Thorough documentation

Burp Suite

Burp Suite is a Java based Web Penetration Testing framework. It has become an industry standard suite of tools used by information security professionals. Burp Suite helps you identify vulnerabilities and verify attack vectors that are affecting web applications. Because of its popularity and breadth as well as depth of features.
Features
- Easy scan set-up
- Recurring scanning
- Out-of-box configurations
- Multi-faceted AST
- Scheduled scanning
- Agent-led scanning
- Custom configurations
- Burp Scanner
OWASP ZAP, short for Zed Attack Proxy, is an open-source web application security scanner. It is intended to be used by both those new to application security as well as professional penetration testers.
It is one of the most active OWASP projects and has been given Flagship status.
When used as a proxy server it allows the user to manipulate all of the traffic that passes through it, including traffic using https.
It can also run in a daemon mode which is then controlled via a REST API.
Features
- Automatic updates and pull request analysis.
- The scalability of this product is very good.
- The reporting is quite intuitive, which gives you a clear indication of what kind of vulnerability you have that you can drill down on to gather more information.
- The OWASP's tool is free of cost, which gives it a great advantage, especially for smaller companies to make use of the tool.
- It can be used effectively for internal auditing.
- The community edition updates services regularly. They add new vulnerabilities into the scanning list.